If you are looking for a new browser to browse more securely and keep your browsing history unknown, maybe Tor (Onion Router) be an option for you. It is a special browser designed for anonymous and protected use Against traffic analysis which can be used for legitimate reasons although it is often associated with darknet and criminal activities. It’s important to make it clear that it’s Tor. not an illegal tool – It has a similar situation to VPNs.
Tor browser was originally designed by United States Navy to protect confidential US government communications. However, over time, it has grown into an open-source cross-platform browser run by a nonprofit and made available to the general computer public (including). macOS operating system and Linux) and systems android.
How does Tor work?
Tor FreeThere are no registration requirements, data caps, advertisements, or requirements to upgrade to a paid product. It uses a technology known asOnion Routing” or “onion routing” (yes, English onion) is designed in such a way that no one can monitor online communication.
“Onion” is based on a peer-to-peer (P2P) overlay network that allows users to browse the Internet anonymously. uses various encryption layers To hide the source and destination of sent information. Servers managed by volunteers from all over the world (also known as “”)relays“) is responsible for sending data to an exit “node”, the point where data leaves the network. After sending, it is encrypted several times before it is sent to the next “node”. The first “protective relay” knows your IP address, but has no other clues about your identity or the website you are accessing. The next steps don’t have any information until we reach the last node, which is the only one who knows the URL.
After “peeling off a few layers of this onion”, the target site sees: HE IP address from the Tor exit node instead of yours. Basically, Tor uses the same basic principle as a VPN service, but with a few differences regarding extra layers of security and technology.

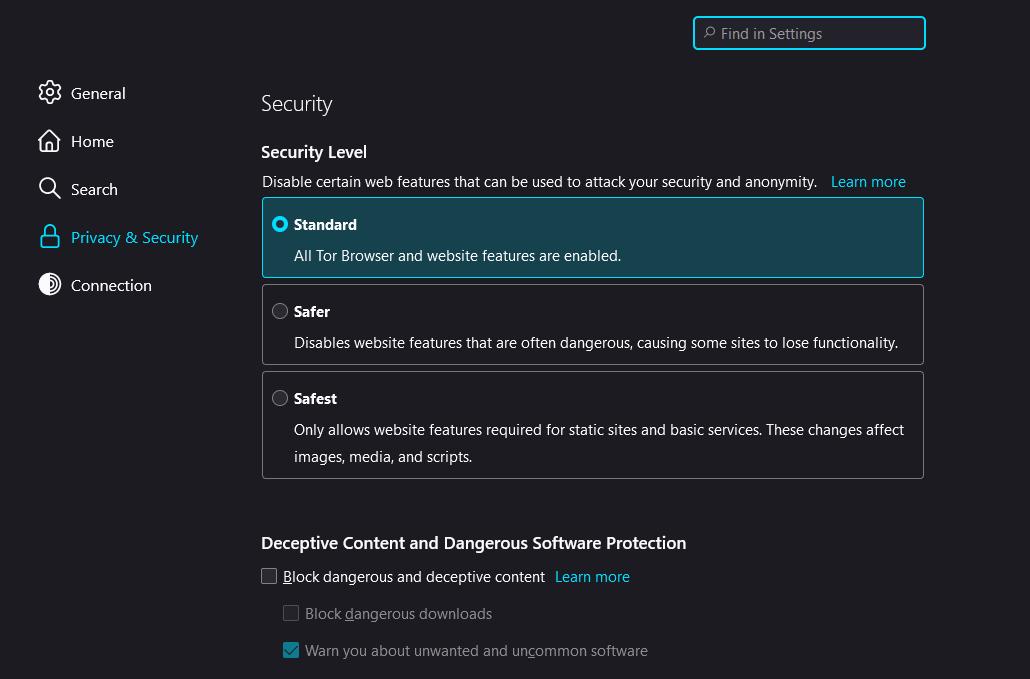
Tor does not monitor browsing history or stores cookies, and offers three levels of security. Each provides a different degree of protection; The “default” level is the easiest but has the lowest security rating. Level 2 is considered safer at cost. a slower experienceand disables some fonts and images in addition to JavaScript on all top-level sites.
How to use Tor
You can download the program compatible with your platform from the official Tor website. Running the installer configures your device with Tor Browser, a special version of Firefox. This includes the extra software required for Tor to work.
Start Tor Browser and it will ask if you want to connect to Tor. click Connect and ready.
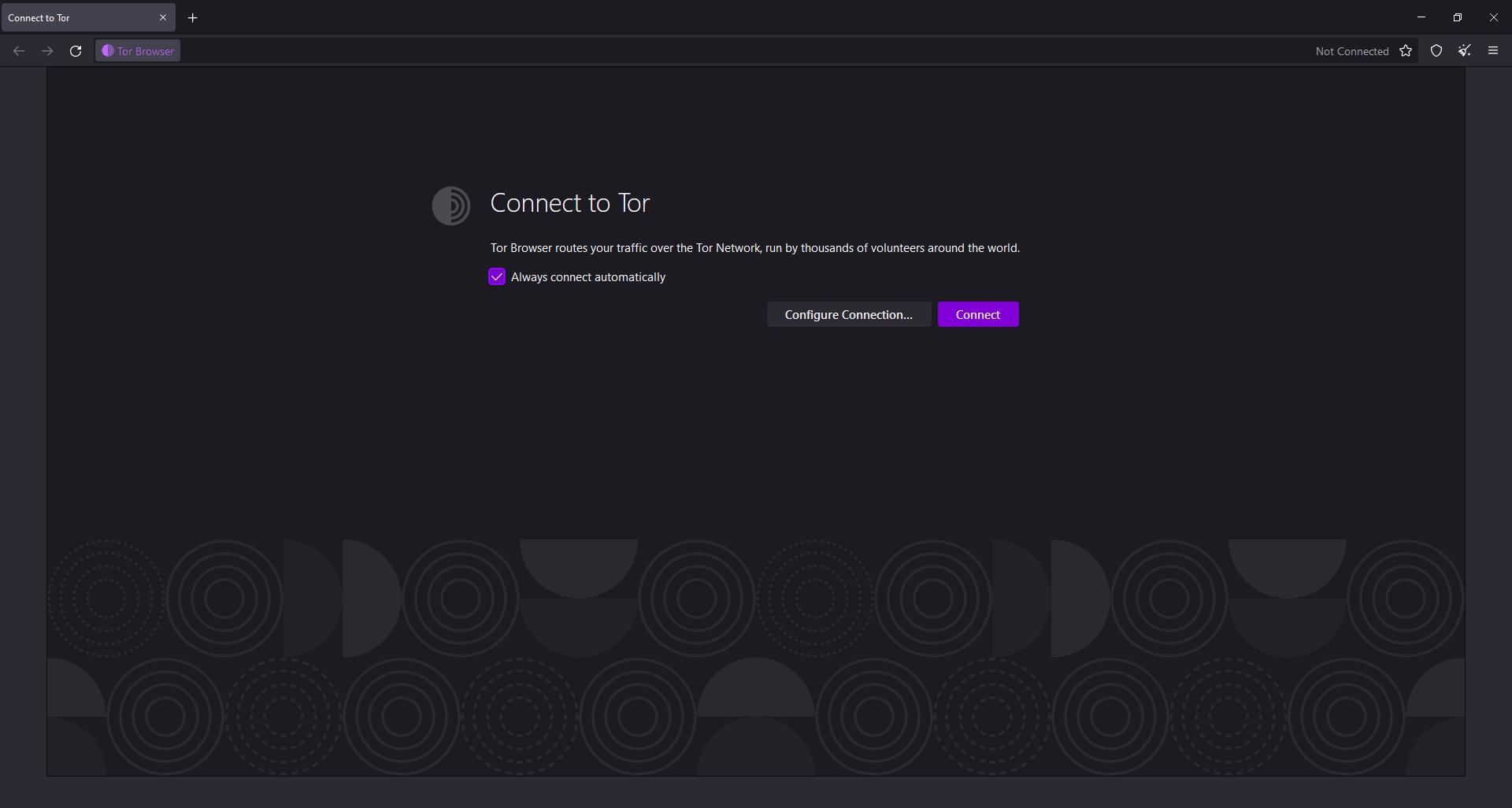
After that, it works like any browser. The only downside is that it’s actually slower than other browsers.
It is worth noting that the browser uses outbound relays and encrypted tunnels to hide user traffic on a network. However, if, for example, someone accesses sites that do not use end-to-end encryption (E2EE), there are several ways law enforcement can track them.
Another important point is Tor. not immune to attacks and espionage, although it is considered more secure than popular browsers. as TechTarget He explains that while this method does not explicitly reveal a user’s identity, blocking traffic can reveal information about the source.
Some websites may also prevent users using the Tor browser from accessing their pages.
Source: Tec Mundo