iOS VPN apps do not encrypt all traffic due to a bug in the system. This was stated by security expert Michael Horowitz.
Once enabled, the VPN device acquires a new IP address and hides all internet connections and then re-establishes them through the VPN. The problem is that iOS does not allow VPN services to close all connections.
For example, the Apple Push connection, through which all settings on iOS are delivered, remains insecure. As a result of the provider and discovery, you can find out the IP address and calculate its location.
Most insecure connections with a running VPN are short-lived and are restored through the VPN tunnel after a few minutes. But in the case of push notifications, Apple’s situation is exacerbated, as these connections can stay connected for hours.
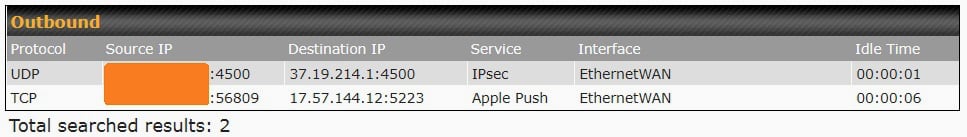
Wired testing using the ProtonVPN app mid 2022 on an iPad running iPadOS 15.4.1. Horowitz also launches OpenVPN with the WireGuard protocol on iPadOS 15.5. His tablet continues to send insecure requests to Apple and Amazon servers.
iOS device output outside the VPN tunnel. It’s a non-classic/fixed DNS leak, it’s a data leak. I have confirmed this using several types of VPN apps from several VPN providers. The latest version of iOS I tested is 15.6.
Michael Horowitz, security expert
For the first time, ProtonVPN managed to collect about this problem in March 2020. They ruled out that the VPN worked in a similar way in iOS 13.3.1 and iOS 13.4.
By October 2020, Apple had not fixed the issue. However, iOS 14 introduced the ability to use the Kill Switch feature, which manually terminates all insecure connections. According to Horowitz, this feature does not work with ProtonVPN.
Horowitz reported the problems to Apple at the end of May. Then the company got in touch, but stopped adding messages. Windscribe co-founder Egor Sak stated that he is aware of the issue, and Windscribe has contacted Apple several times about resolving it. [ArsTechnica]
Source: Iphones RU