Today, most Internet users are aware of the dangers and risks of using network technologies. To protect many solutions from fees, antivirus and system fees.
We do not even think about what algorithms protect us while using the network and take it for granted. However, about 40 years ago, atmospheric patients did not.
An ordinary student could bring down a network of many thousands with a few lines of code. About such a story, which was the first case of the use of the virus, we will consider in this article.
How did computer viruses originate?

Currently available to a limited number of users. These were scientists and representatives of military organizations. None of them thought of pests that cause harm to the health of colleagues or users of the public network.
For a long time, large networks grew only within one country, and access to them was carried out through a limited number of terminal PCs. Access to such a computer was clearly controlled and imperceptibly harmed other users, it was very difficult.
To the point: Where did the first Internet browsers come from? One of them was made by Steve Jobs.
In the 80s, large networks began to cover several states, and were connected to some business representatives, financial institutions and individual users. It has become commonplace to detect viruses and other malicious code.
Entrepreneurial researchers discover attacks on other network users, get reliable information, or disrupt some organization. The cases of attacks were sporadic and did not particularly bother the administrators of the growing global network.
Who invented the first virus

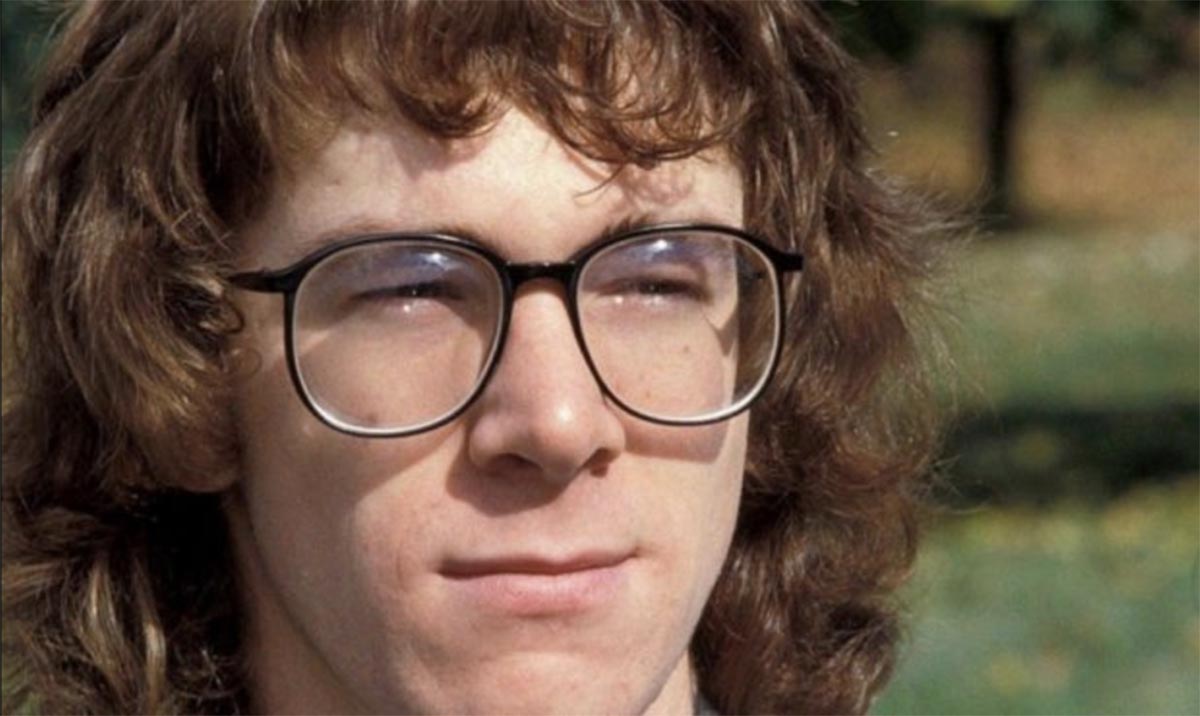
Robert Morris (photo 1989)
In the second half of the 80s, two heavy networks competed with each other: diabetic by the US military ARPANET and created for scientific purposes NSFnet. Each of the networks has its own advantages and in the future can become a pillar for the modern Internet.
To the point: How the Internet was born 52 years ago and how it evolved
However, the first network virus intervened in the work of one of them. Young enthusiast Robert Morris launched a viral code that caused multi-million dollar damage.
The 23-year-old’s father was a cryptography expert who worked for government organizations and was involved in the development of source systems. Multix and Unix. The son followed in the footsteps of his parent and began to take an active interest in computer technology.
While Robert Morris with honors from school and comprehended computer science at one of the US universities. In their free time, classes took up the formation of the first network virus.
What was the Morris virus: malicious code or a network experiment
Robert Morris I immediately found several vulnerabilities in the descriptions of applications and communication protocols. He decided to use them for a major network experiment. ON THE OCCASION of the observed size of the network and taking into account many of its parameters.
the use of the code was designed to account for users, but ultimately harmed the network and the personal computers on it.
Software Morris was expected to run on computers WACS and SUN governed by BSD UNIX. A hole in the security utility was used to transfer the code Send mailwhich at that time was widely used for e-mail exchange.
Maurice managed to write code that distributed the credentials and passwords of other network users. As you know, Robert’s specialists did not do anything supernatural, but simply guessed to use the obvious problems and imperfections of the software of that time.
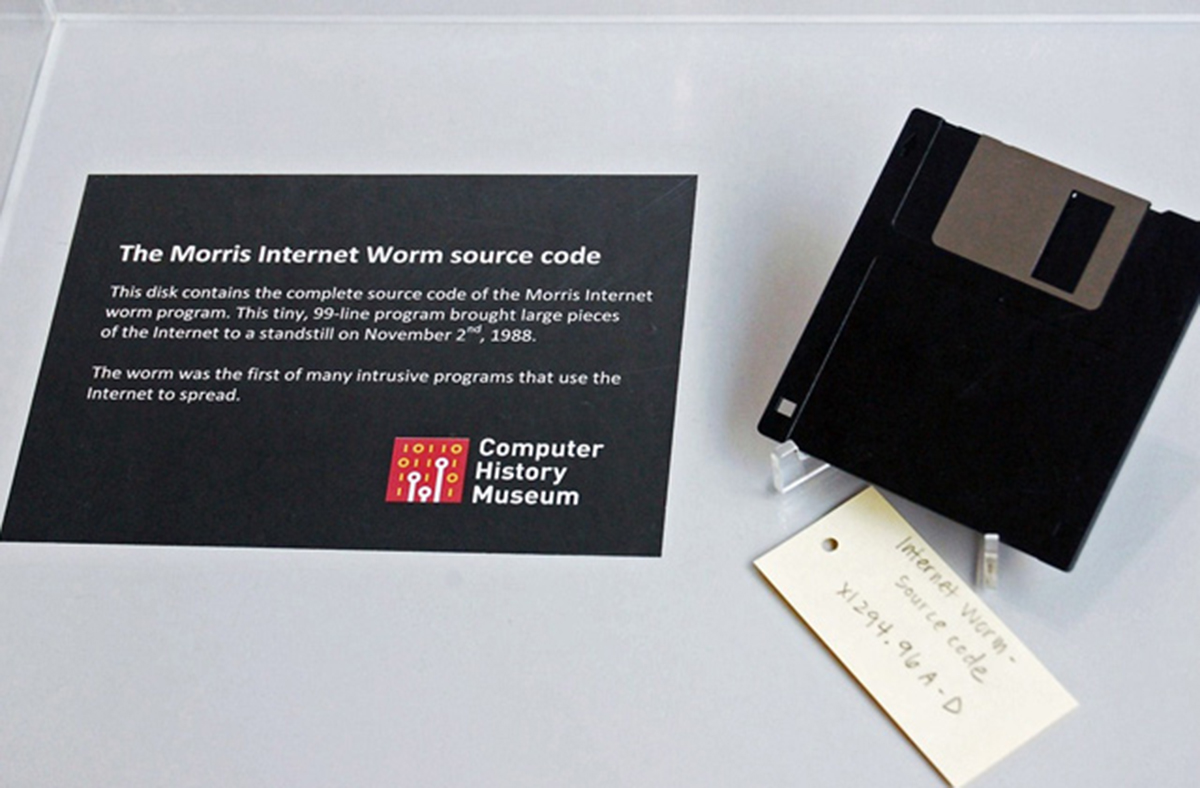
Morris virus source code on a floppy disk at the Computer History Museum
accusers Morris it was revealed that the virus originated as a virus, because he developed a good security system for his software. Version 1 code did not run if it was already seen to be running on the new machine.
So, according to Morris, system administrators could trick the virus and stop its spread. Ultimately, the code was implemented and could work even in cases where it already looked on the computer.
Ultimately, the launch of several copies of the virus on different computers had a strong impact on the network and could literally paralyze it.
All data about the virus is stored in RAM and does not leave investigators on drives, complicates the search and counteraction on the part of system administrators. As soon as the computer disconnected from the network and rebooted, it did not follow the Morris code, but within a few minutes after connecting to the network, the PC was infected again.
All observations were found on the network, infected computers that monitored the presence of new connected and removed from many copies of viruses to all subscribers.
Another argument against Morris was the first run of malicious code. Robert studied at Cornell Universityactivated his virus while on campus tours Massachusetts Institute of Technology (MIT).
Who should unexpectedly secretly launch software that has scientific and educational goals?
What harm did the Morris worm do

In just a few days, the virus spread throughout the computer network, which consisted of the next thousand computers. Malicious activity, on the other hand, affects the network and immediately attracts a large number of participants to negotiate with it.
For 12 hours Active work and study of the program code included a closed hole for free and began to distribute it over the network. Unfortunately, the virus itself did it quickly.
The increased workload literally brought it down in the narrowest places and the most distant seats that could not be connected to receive upgrade packages.
Morris himself was frightened by the scale of his work and offered to rectify the situation. He did not lay down the so-called “breaker” for the rapid detection of the virus, but had a plan in mind to neutralize it. Morris could not personally declare what had happened and help stop the online epidemic, he offered to publish an anonymous apology and lay out instructions for “treatment”.
The problems were solved by specialists from the National Computer Security Center, the Institute of State Science and Technology, the Military Communications Agency, the US Department of Energy, the CIA, the FBI and other US organizations. As you remember, the network chosen for the attack by Morris ARPANET stunned the Travelers and military institutions of the country.
The virus was sorted out in a few days and they began to count external damage.
Analysts believe that the harm was initial approximately 6000 computerswhich is about 10% of all devices online at the time. Damage to each device was assessed from $200 to $50 thousand depending on the importance of the stored data.
In the end, the estimated cost of total damage was announced from $100 thousand to $10 million. A search and identification of the perpetrator of the incident began.
The punishment for the world’s first online scammer has been severely mitigated
Robert Morris with his lawyer
The story is silent about exactly how Morris managed to find him and associate him with the running virus. It is believed that he persuaded his father personally to Vina Robert.
At that time, Morris held a senior management position in the IT security division of the US federal government. The antics of the son might then cast a shadow over the loss of the father.
Finally Robert Morris became first person to be blamed in new computer accident article. The maximum rating level is 8 deprivation of liberty up to five years and fine up to $250.

Robert Morris passes the courthouse, accompanied by his mother and lawyer
Robert went to join the investigation and received a more significant lenient sentence. The guy was awarded three years probation, a $10,000 fine and 400 hours of work.
Such a decision was made, after considering that Morris had no criminal malicious intent and he did not hide his involvement in the deed. In defense of condemnation, the developers of the utility are also subjected to Send mail, which was distributed by the Australian code. Programmers believe that a number of vulnerabilities have been identified and a set of publicly available tools that are on the surface are being used.
What are the consequences of launching the Morris virus
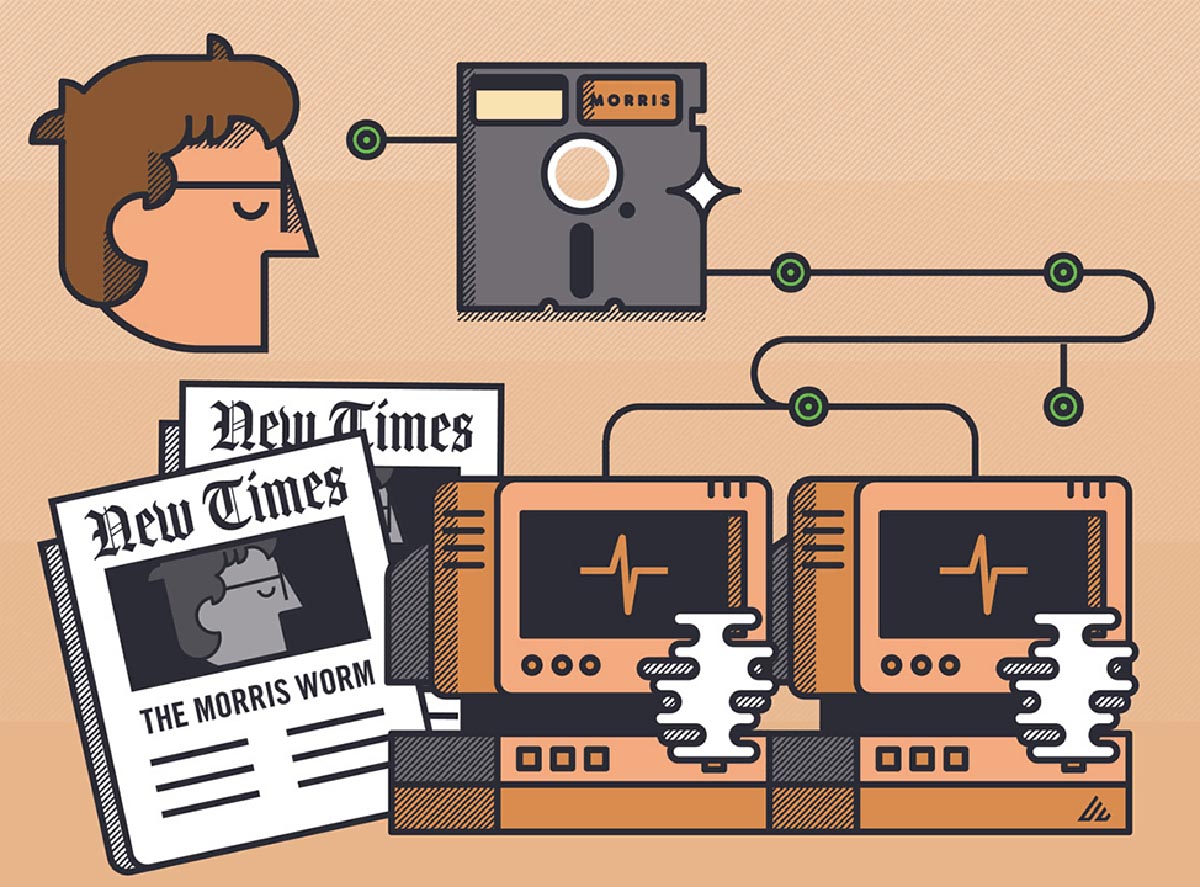
Journalists New York Times speculated that Morris was triggered by the influence of a sci-fi novel Shockwave Rider John Brunner. In it, the heroes used a worm program to disable the construction of an authoritarian enemy supercomputer.
It was because of this connection with the production of the virus that Morris began to reproduce as a worm.
So in the confrontation between the two networks, the scales tipped to the side NSFnet. A more cumbersome and clumsy government network ARPANET although it survived a major attack by the Morris worm, it has already experienced an outflow of users.
In 1990 the network NSFnet started talking Interneta ARPANET officially broad ownership.
One of the first cases of virus infection in the media
At the same time, administrators and authorities received a clear example of the insecurity of networks. Later, many organizations appeared that were engaged in improving the security of communication protocols and the development of protection against harmful substances in software.
Until the discovery of the Morris worm, no one seriously knew about the network security of computers, and after this connection, several related IT industries appeared.
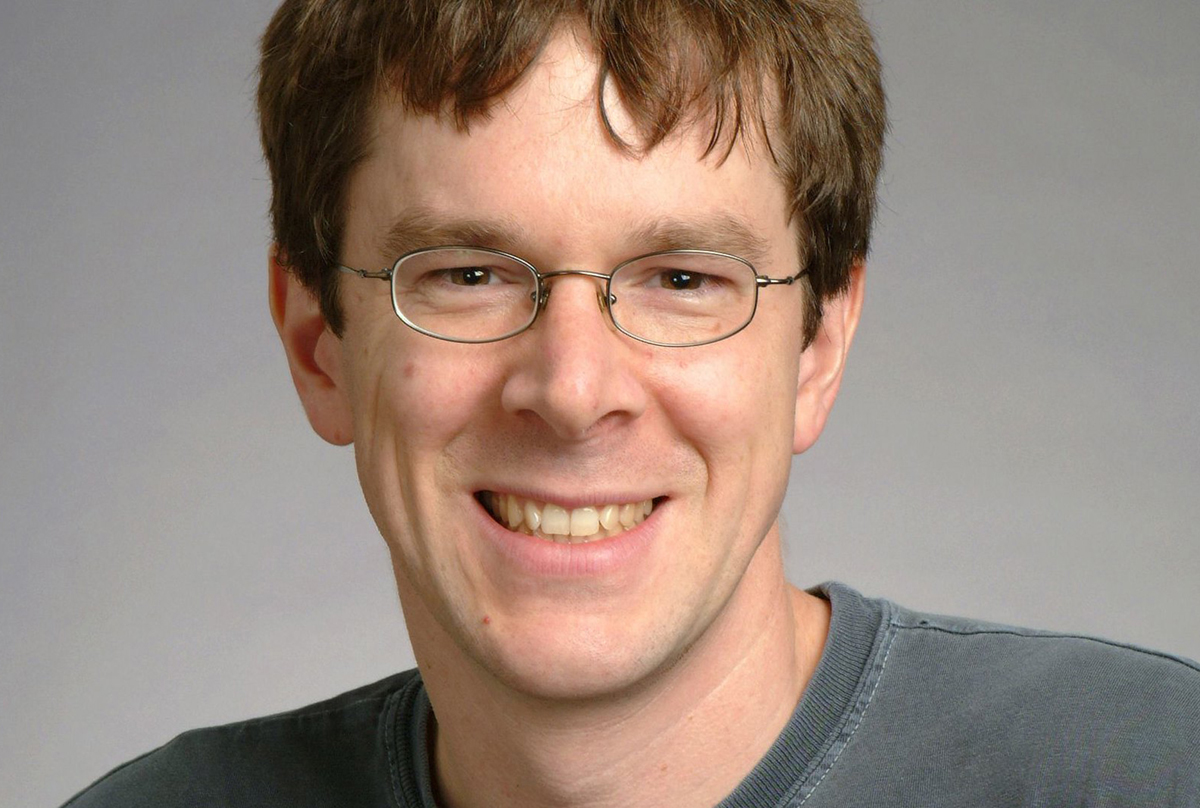
Morris, engaged in scientific activities
Morris himself continues to work in the field of computer technology, after several years of the existence of his own startup. viawebwhich was subsequently sold to the company Yahoo! for almost $50 million
After that, Robert found himself in science, received his degree and began academic value. Since 2019, Morris has held a position in US National Academy of Engineering.
This story was partly laid down in the script of the feature film. hackers 1995 (director Ian Softley). The tape has become an important feature in the films of rising Hollywood stars. Angelina Jolie.
Source: Iphones RU










