With this striking title, if you have any knowledge of technology, you may have recognized what it refers to. For those who don’t know, a new method SATAn is essentially a way to steal information and data from secure systems over the air using a SATA cable as a wireless antenna. to transfer data and information from a PC to a device in a nearby location.
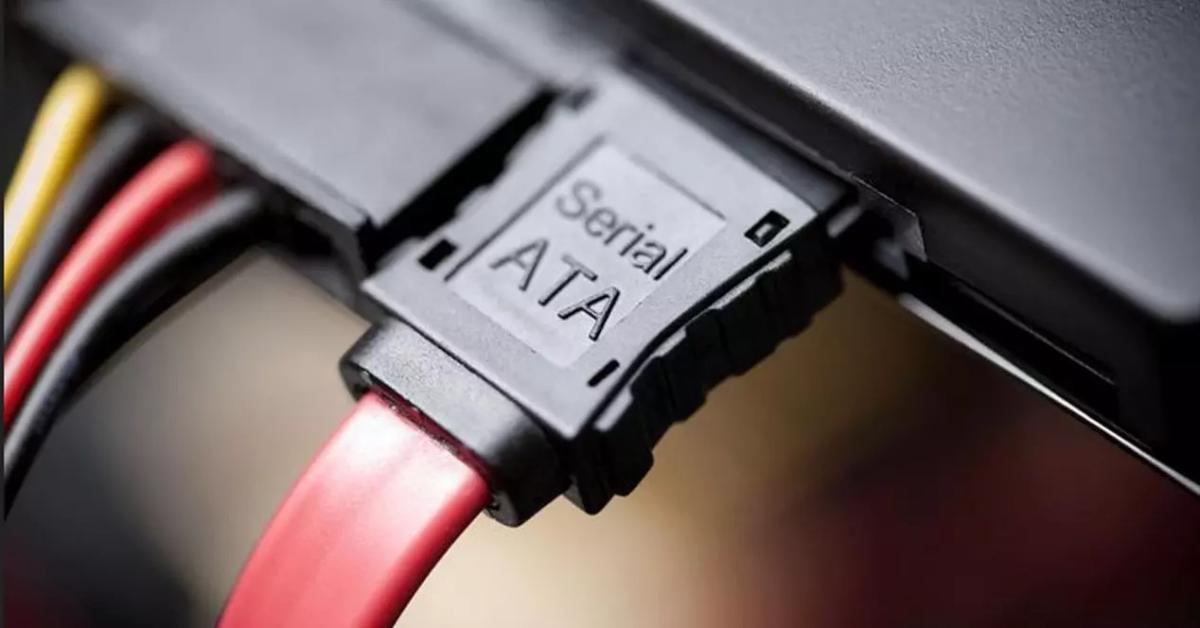
The SATA (Serial Advanced Technology Attachment) cable is an element that physically connects the motherboard to storage devices. We will discover this very easily if we open up our computer tower, and they served to increase the speed and bandwidth of data transfer compared to the connectors that were previously used.
This type of hack arises from the need to steal highly secure data belonging to air-tight systems or networks that are isolated from any connection to the rest of the world (no internet, no Bluetooth). That’s why another form of security breach is needed.
It’s very hard to crack them. but we already see that it is not impossible and the answer is SATAn. And the fact is that in this process it all comes down to the manipulation of electromagnetic interference thanks to this cable.
During the test, in order to analyze how this system actually works and thus makes the protected system vulnerable, the researcher manipulated these electromagnetic interference and used a SATA cable as a makeshift 6 GHz wireless antenna.
“The receiver monitors the 6 GHz spectrum for possible transmission, demodulates the data, decodes it, and sends it to the attacker.”explains the researcher in his article.
They specify that this attack requires pre-installation of malicious software to complete the whole process. Perhaps this may be the most difficult part, since without it it is impossible to steal data through SATAn.
Now don’t panic. Given the complexity of the attack, only those who had very broad knowledge in this area could conduct it. In addition, this is done only with systems that really have something to hide.
Source: Computer Hoy
I am Bret Jackson, a professional journalist and author for Gadget Onus, where I specialize in writing about the gaming industry. With over 6 years of experience in my field, I have built up an extensive portfolio that ranges from reviews to interviews with top figures within the industry. My work has been featured on various news sites, providing readers with insightful analysis regarding the current state of gaming culture.